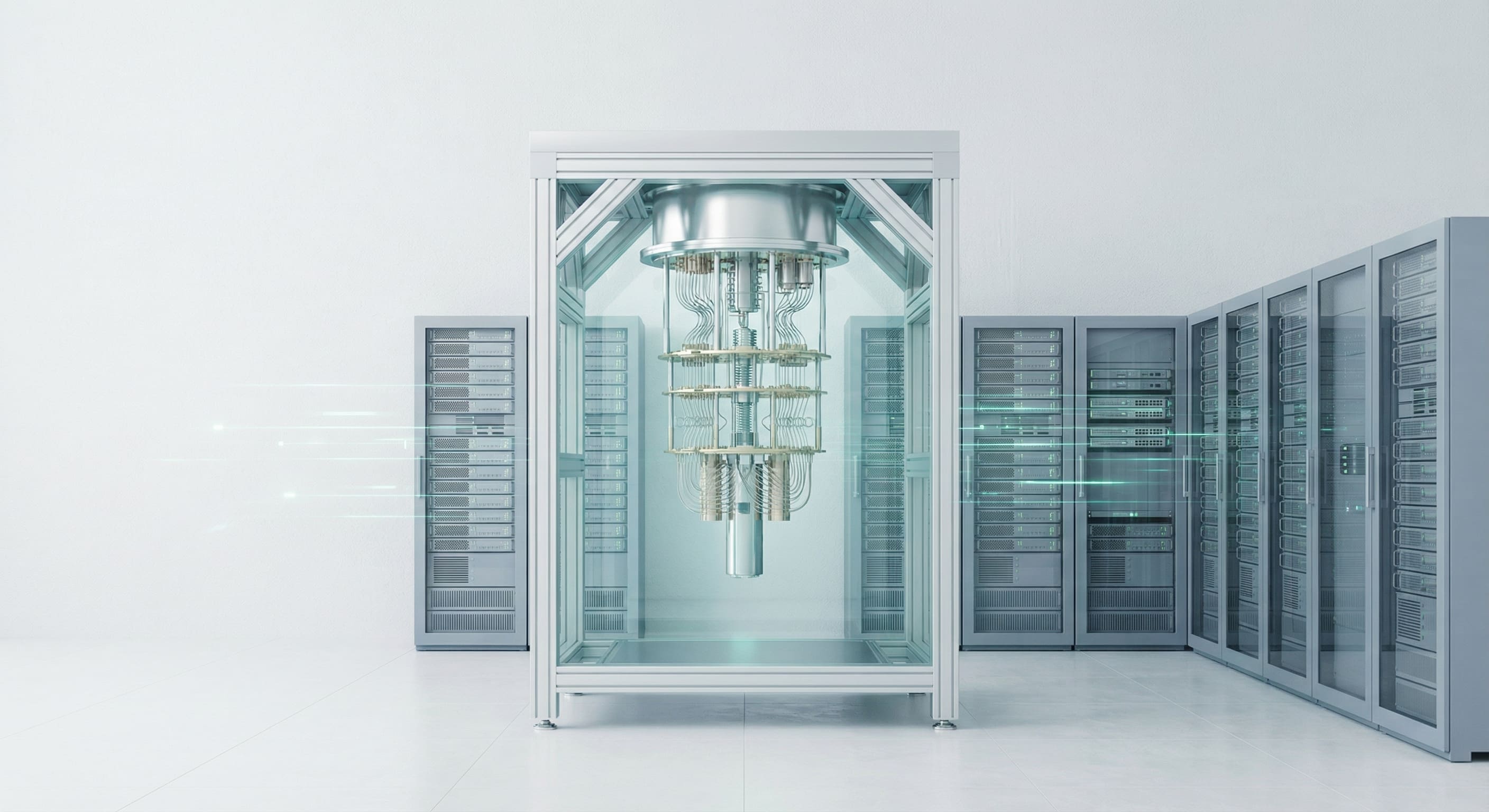
Quantum Computing Is Reshaping Digital Security
For decades, digital security has been built on mathematical problems that are difficult for classical computers to solve. Encryption, authentication, and secure communication across the internet rely on this asymmetry between what is easy to compute and what is computationally infeasible to break. Quantum computing is fundamentally changing that assumption.
As quantum technology advances, it is reshaping how organisations must think about digital security, not as a distant theoretical concern, but as a strategic issue that requires action today.
Why Quantum Computing Changes the Security Model
Classical encryption schemes such as RSA and ECC rely on problems like integer factorisation and discrete logarithms. These problems are computationally expensive for traditional computers, which is why they have formed the backbone of secure digital communication for decades.
Quantum computers operate differently. By leveraging quantum properties such as superposition and entanglement, they can solve certain classes of problems exponentially faster than classical systems. Algorithms such as Shor's algorithm demonstrate that a sufficiently powerful quantum computer could break widely used public-key cryptography in a fraction of the time previously required.
This does not mean that all encryption will suddenly fail overnight. However, it does mean that the long-term security assumptions underlying today's digital infrastructure are no longer guaranteed.
The "Harvest Now, Decrypt Later" Risk
One of the most immediate security concerns is not future attacks, but present-day data collection. Encrypted data intercepted today can be stored and decrypted later once quantum-capable systems become available.
For organisations handling sensitive information with long confidentiality requirements, such as financial data, intellectual property, critical infrastructure data, or personal records, this represents a significant risk. Information that must remain secure for ten, twenty, or thirty years is already exposed if protected solely by quantum-vulnerable cryptography.
This shifts the timeline for action. Preparing for quantum security is not about reacting to a future event, but about protecting data that exists now.
Post-Quantum Cryptography and Algorithm Agility
The primary response to quantum threats is the development of post-quantum cryptography. These are cryptographic algorithms designed to be secure against both classical and quantum attacks.
However, replacing cryptography is not simply a matter of swapping algorithms. Enterprise systems are deeply embedded with encryption at multiple layers, including communication protocols, identity management, storage, and APIs. A resilient approach requires algorithm agility, the ability to update cryptographic mechanisms without redesigning entire systems.
Organisations that invest in flexible architectures today will be better positioned to adopt post-quantum standards as they mature and are formally standardised.
Impact on Enterprise Architecture and APIs
Quantum security implications extend beyond encryption libraries. Modern enterprises rely heavily on APIs and distributed systems, where secure authentication and data exchange are critical.
As quantum-resistant mechanisms are introduced, enterprises must ensure that API security, key management, and identity systems can evolve without disrupting operations. This requires strong governance, centralised security controls, and clear separation between cryptographic mechanisms and business logic.
Enterprises that treat security as an architectural concern rather than a technical afterthought will adapt more effectively to the quantum transition.
A Strategic Shift, Not a Technical Upgrade
Quantum computing is reshaping digital security at a strategic level. It challenges long-held assumptions about trust, longevity of data protection, and risk management.
Forward-looking organisations are already:
- Assessing where quantum-vulnerable cryptography is used
- Identifying data with long-term confidentiality requirements
- Designing systems with cryptographic flexibility and upgrade paths
- Monitoring standards development in post-quantum security
This is not about adopting experimental technology prematurely, but about ensuring that today's digital foundations remain secure in tomorrow's computational reality.
Looking Ahead
Quantum computing will not replace classical computing, but it will redefine the boundaries of what is computationally possible. Digital security must evolve accordingly.
Enterprises that begin preparing now will avoid rushed transitions later, protect sensitive information over its full lifecycle, and maintain trust in an increasingly complex digital ecosystem. In this sense, quantum computing is not just reshaping security technology, it is reshaping how organisations plan for the future of trust itself.